The explosive growth of digital connectivity brought responsive, convenient, and personalized services to consumers. However, it has also brought new ways to fool people, to steal someone’s identity, and to misuse personal data.
To reduce the risk of such harmful activities, organizations implement checkpoints in websites and applications to verify the identity of those who avail of their services. Apart from being a hassle for the users, the effectiveness of this method in ensuring digital security is highly limited.
From our partners:
Now that the world is going online, addressing this problem is important. There is a need to establish digital identity that is reliable and trustworthy.
In the World Economic Forum’s (WEF) white paper, Reimagining Digital Identity: A Strategic Imperative, methods that can transform digital identity and digital identification as we know it were tackled. Let’s discuss each one by one.
Design
Right now, users have to repetitively verify their identities whenever they have to transact with a new site or company. This is highly inefficient given that businesses of the same sector typically demand the same information from their users.
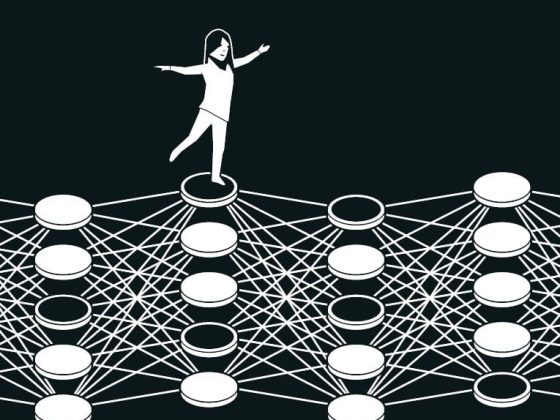
Instead of this siloed approach to digital identity, a collaborative ecosystem can be used so that a person’s digital identity is centralized across business units and sectors.
Ownership
In connection to the unified approach in dealing with a person’s online identity is also a shift in the ownership of the latter. WEF noted that right now, businesses “own” the identity of its users. In order to improve their experience, users should take ownership of the digital identity, something like a digital ID. The personal information that is consolidated in a person’s digital identity are then used to make transactions.
Reputation
In spite of being convenient, digital transactions are notorious for cases of identity fraud and other security issues. The centralization of digital identity should also be combined by increased efforts to make the digital ecosystem a platform worthy of being trusted security-wise.
Value
Right now, the notion of digital identity is of little value given how fragmented our existing digital ecosystem is. We can amplify the value of transforming digital identity if businesses will work together to enhance interoperability and to create an ecosystem that can better cater to the needs of the users.
User Centricity
The focus of businesses is how profit can be further maximized instead of how the user experience can be enhanced. With this, even the information that the customers supply is being used as a competitive advantage. This misprioritisation, needless to say, negatively impacts a user’s transaction.
If we want to make digital identity secure and truly for the users, companies should also empower the users by letting them know and choose what kind of information they give out. This transparency and control is another way the trust on digital security can be boosted.
Breaking walls
“We need a new model that starts with the commitment to the fundamental individual right – ‘I own my identity and I control my identity data.’ And we need businesses, governments, NGOs and others to forge partnerships and invest resources in support of a common framework, principles and standards,” Mastercard Cyber & Intelligence President Ajay Bhalla, said.
Truly enough, the only hurdle along the way of attaining genuine digital identity are the walls that we ourselves have set up in our traditional business frameworks.
While these frameworks may have worked during their time, they’re nothing more but a thing of the past in the context of our digital world. It is about time to accept this reality and finally move on.
For enquiries, product placements, sponsorships, and collaborations, connect with us at [email protected]. We'd love to hear from you!
Our humans need coffee too! Your support is highly appreciated, thank you!