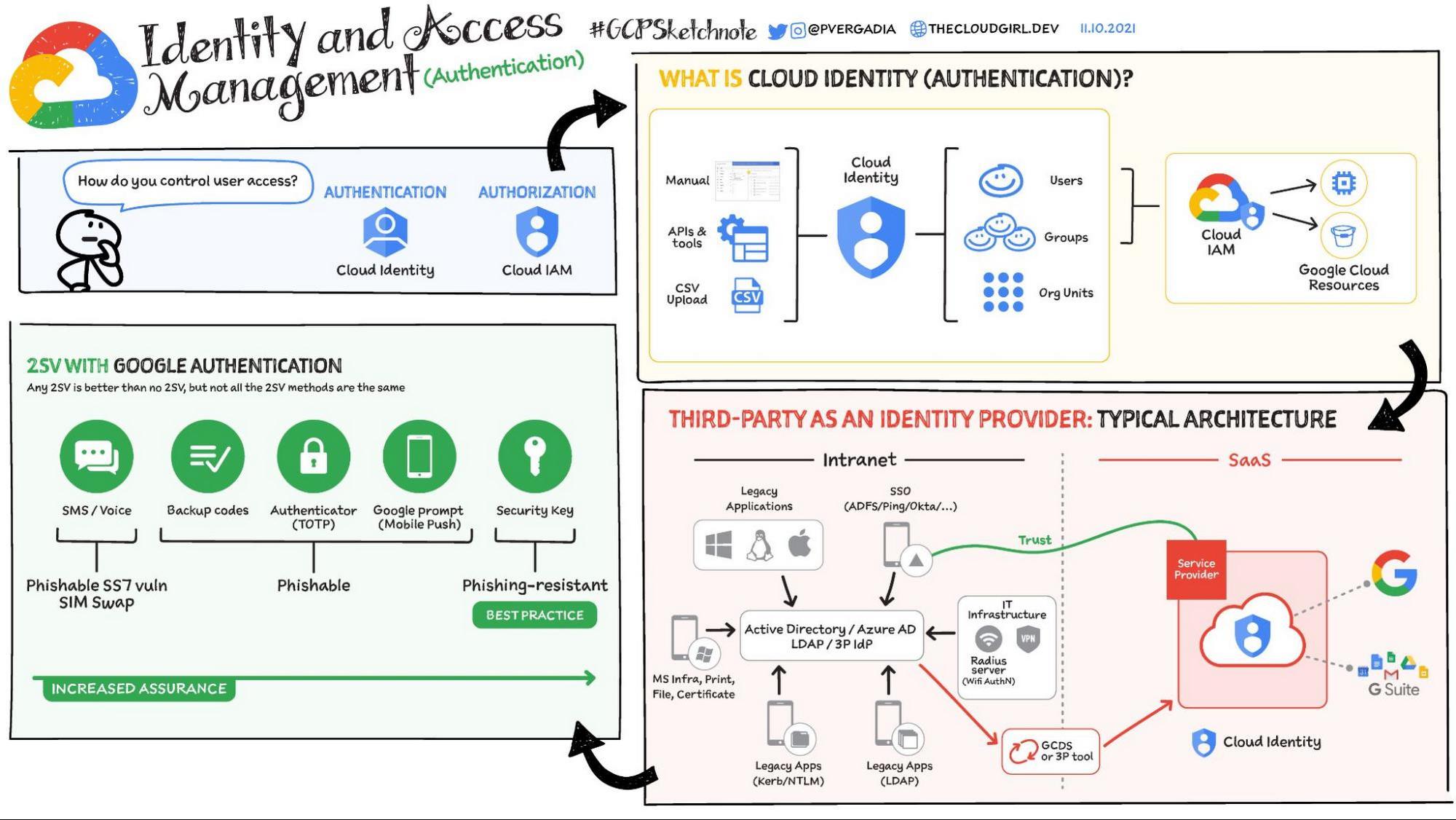
Identity & Access Management: Authentication With Cloud Identity
In security, the three “A”s of controlling access are Authentication (Who is the user?), Authorization (What is the user allowed to do?), and Auditing (What are they doing?) Going a…
Share