Use OpenWRT and Wireguard to create your own virtual private network on your router.
Getting from one place to another over a computer network can be a tricky thing. Aside from knowing the right address and opening the right ports, there’s the question of security. For Linux, SSH is a popular default, and while there’s a lot you can do with SSH it’s still “just” a secure shell (that’s what SSH stands for, in fact.) A broader protocol for encrypted traffic is VPN, which creates a unique, virtual private network between two points. With it, you can log in to a computer on another network and use all of its services (file shares, printers, and so on) just as if you were physically sitting in the same room, and every bit of data is encrypted from point to point.
From our partners:
Normally, in order to make a VPN connection possible, the gateways into each network must accept VPN traffic, and some computer on your target network must be listening for VPN traffic. However, it’s possible to run your own router firmware that runs a VPN server, enabling you to connect to your target network without having to worry about forwarding ports or thinking at all about internal topography. My favorite firmware is OpenWrt, and in this article I demonstrate how to set it up, and how to enable VPN on it.
What is OpenWrt?
OpenWrt is an open source project that uses Linux to target embedded devices. It’s been around for more than 15 years and has a large and active community.
There are many ways to use OpenWrt, but its main purpose is in routers. It provides a fully writable filesystem with package management, and because it is open source, you can see and modify the code and contribute to the ecosystem. If you would like to have more control over your router, this is the system you want to use.
OpenWrt supports many routers, including famous brands such as Cisco, ASUS, MikroTik, Teltonika Networks, D-Link, TP-link, Buffalo, Ubiquiti, and many others.
What is Wireguard?
Wireguard is open source virtual private network (VPN) software that is much faster, simpler, and more secure than other options such as OpenVPN. It uses state-of-the-art cryptography: ChaCha20 for symmetric cryptography; Curve 25519 (which uses elliptic curves) for key agreement; and BLAKE2 for hashing. These algorithms are designed in a way that is efficient on embedded systems. WIreguard is also available on a wide variety of operating system platforms.
Prerequisites
For this project, you will need:
- Teltonika RUT955 or another router supported by OpenWrt
- A public IP address to connect to your VPN from outside your network
- An Android phone
Install OpenWrt
To get started, download the OpenWrt image for your router. Use the firmware selector to check if OpenWrt supports your router and download the firmware. Enter your router’s model, and it will show your options:
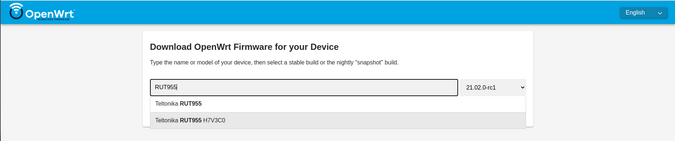
(Lukas Janenas, CC BY-SA 4.0)
Select the firmware version you want to download by using the drop-down input on the right side of the search box.
Download the factory image.
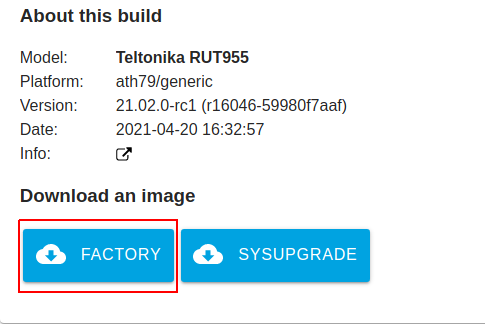
(Lukas Janenas, CC BY-SA 4.0)
Many routers allow you to flash unauthorized firmware from the web interface, but Teltonika Networks does not. To flash the OpenWrt firmware to a router like this, you need to use the bootloader. To do so, follow these steps:
- Unplug the router’s power cable.
- Press and hold the Reset button.
- Plug in the router’s power cable.
- Continue holding the reset button for 5 to 8 seconds after you plug the power cable in.
- Set computer’s IP address to
192.168.1.15and the netmask to255.255.255.0. - Connect the router and your computer with an Ethernet cable over a LAN port.
- Open a web browser and enter
192.168.1.1:/index.html. - Upload and flash the firmware.
The flashing process can take up to three minutes. Afterward, you should be able to reach the router’s web interface by entering 192.168.1.1 in a browser. There is no password set by default.
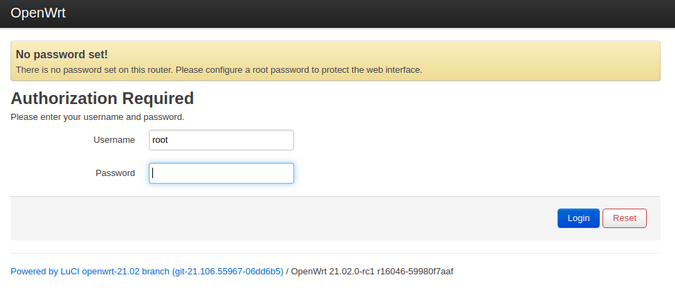
(Lukas Janenas, CC BY-SA 4.0)
Configure network connectivity
Network connectivity is a requirement. If your Internet service provider (ISP) assigns your IP address automatically using DHCP, you just need to plug your Ethernet cable into the WAN port of your router.
If you need to assign the IP address manually, navigate to Network → Interfaces. Select Edit to edit your WAN interface. From the Protocol field, select Static address, and select Switch protocol.
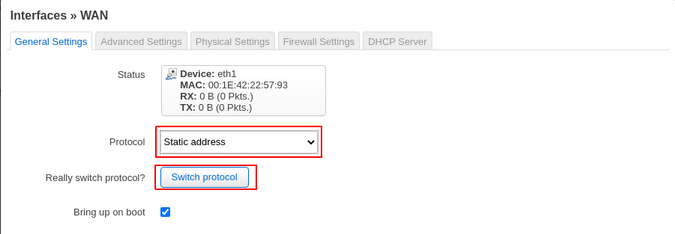
(Lukas Janenas, CC BY-SA 4.0)
In the IPv4 address field, enter your router’s address. Set IPv4 netmask to match your network subnet; enter the IPv4 gateway address you will use to connect to the network; and enter the DNS server’s address in the Use custom DNS servers field. Save the configuration.
That’s it! You have successfully configured your WAN interface to get network connectivity.
Install the necessary packages
The firmware doesn’t include many packages by default, but OpenWrt has a package manager with a selection of packages you can install. Navigate to System → Software and update your package manager by selecting Update lists…
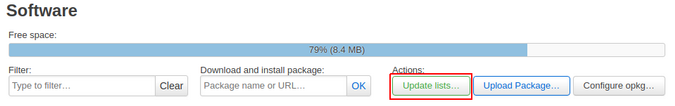
(Lukas Janenas, CC BY-SA 4.0)
In the Filter input, type Wireguard, and wait until the system finds all the packages that include this keyword. Find and install the package named luci-app-wireguard.
(Lukas Janenas, CC BY-SA 4.0)
This package includes a web interface to configure Wireguard and installs all the dependencies necessary for Wireguard to work.
If you get a warning that a package is missing and can’t be found in the repositories before installing the Wireguard package, just ignore it and proceed.
Next, find and install the package named luci-app-ttyd. This will be used to access the terminal later.
After these packages are installed, reboot your router for the changes to take effect.
Configure the Wireguard interface
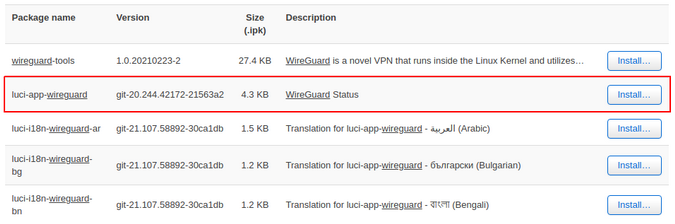
Next, create the Wireguard interface. Navigate to Network → Interfaces and select Add new interface… on the bottom-left. In the pop-up window, enter your desired name for the interface, choose Wireguard VPN from the drop-down list, and select Create interface on the lower-right.

(Lukas Janenas, CC BY-SA 4.0)
In the new pop-up window, select Generate Key to generate a private key for the Wireguard interface. In the Listen Port field, enter your desired port. I will use the default Wireguard port, 51820. In the IP Addresses field, assign the IP address which will be used for the Wireguard interface. In this example, I use 10.0.0.1/24. The number 24 indicates the size of my subnet.
(Lukas Janenas, CC BY-SA 4.0)
Save the configuration and restart the interface.
Navigate to Services → Terminal, log into the shell, and enter the command wg show. You will see some information about your Wiregaurd interface, including its public key. Copy down the public key—you will need it to create peers later.

(Lukas Janenas, CC BY-SA 4.0)
Configure the firewall
Navigate to Network → Firewall and select the Traffic Rules tab. On the bottom of the page, select Add. In the Name field of the pop-up window, give your rule a name, e.g., Allow-wg. Next, change the Destination zone from Lan to Device, and set the Destination port to 51820.
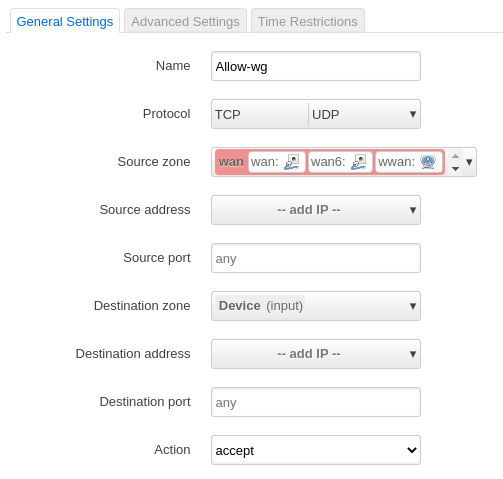
(Lukas Janenas, CC BY-SA 4.0)
Save the configuration.
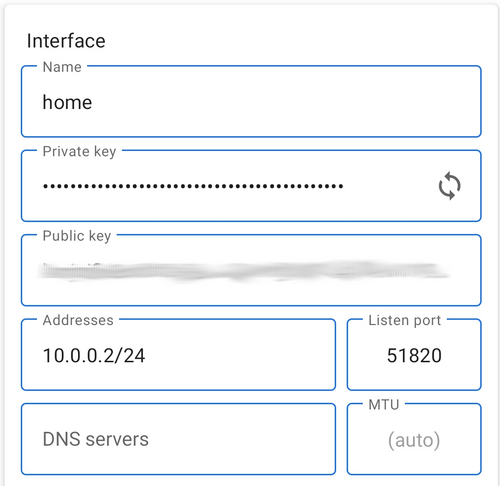
Configure Wireguard on an Android phone
Install the Wireguard app on your phone from Google Play. Once it’s installed, open the app and create a new interface from scratch. In the Name field, enter the name you want to use for your interface. In the Private key field, press the double-arrow icon on the right to generate a key pair. You will need the public key from above to create a peer between your phone and router. In the Addresses field, assign the IP address you will use to reach the phone over VPN. I will use 10.0.0.2/24. In Listen port, enter a port; I will again use the default port.
Save the configuration.
To add a peer to the configuration, select Add peer. In the Public key field, enter your router’s Wireguard public key. In the Endpoint field, enter your router’s public IP address and port separated by a colon, e.g., 12.34.56.78:51820. In the Allowed IPs field, enter the IP addresses you want to reach through the Wireguard interface. (You can enter your router’s VPN interface IP address and LAN interface address.) The IP addresses must be separated by commas. You can also define the size of the subnet.
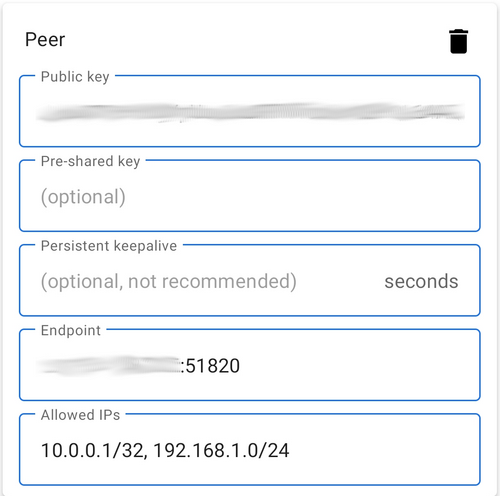
(Lukas Janenas, CC BY-SA 4.0)
Save the configuration.
There’s one last step left in the configuration: adding a peer on the router.
Add a peer on the router
Navigate to Network → Interfaces and select your Wireguard interface. Go to the Peers tab and select Add peer. In the Description field, enter the peer’s name. In the Public Key field, enter your phone’s Wireguard interface public key, and in the Allowed IPs field, enter your phone’s Wireguard interface IP address. Check the Route Allowed IPs checkbox.
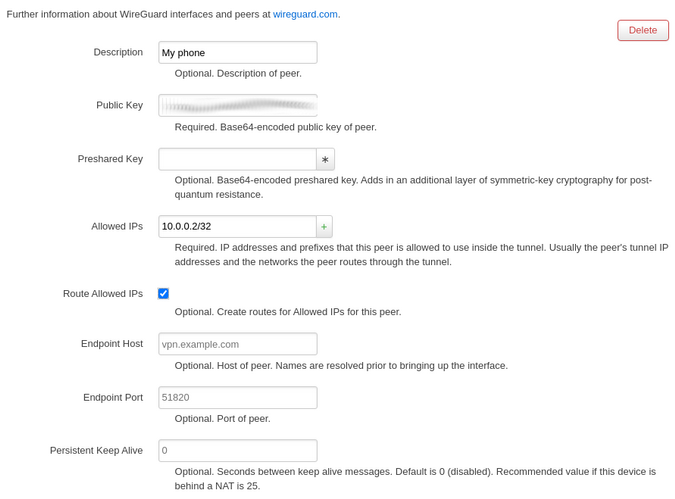
(Lukas Janenas, CC BY-SA 4.0)
Save the configuration and restart the interface.
Test the configuration
Open a web browser on your phone. In the URL bar, enter the IP address 10.0.0.1 or 192.168.1.1. You should be able to reach your router’s website.
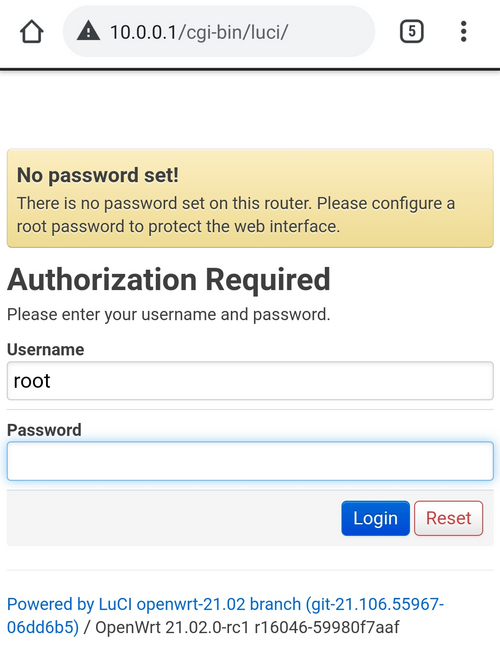
(Lukas Janenas, CC BY-SA 4.0)
Your very own VPN
There are lots of VPN services being advertised these days, but there’s a lot to be said for owning and controlling your own infrastructure, especially when that infrastructure only exists to boost security. There’s no need to rely on somebody else to provide you with a secure connection to your data. Using OpenWrt and Wireguard, you can have your own open source VPN solution.
This piece is republished from opensource.com
For enquiries, product placements, sponsorships, and collaborations, connect with us at [email protected]. We'd love to hear from you!
Our humans need coffee too! Your support is highly appreciated, thank you!