What is Artifact Registry?
Artifact Registry is the recommended service for storing and distributing images and application artifacts in Google Cloud. It provides a single location for storing and managing your packages and Docker container images. Artifact Registry integrates with Cloud Build and other continuous delivery and continuous integration systems to store packages from your builds. You can also store trusted dependencies that you use for builds and deployments.
From our partners:
What is Binary Authorization?
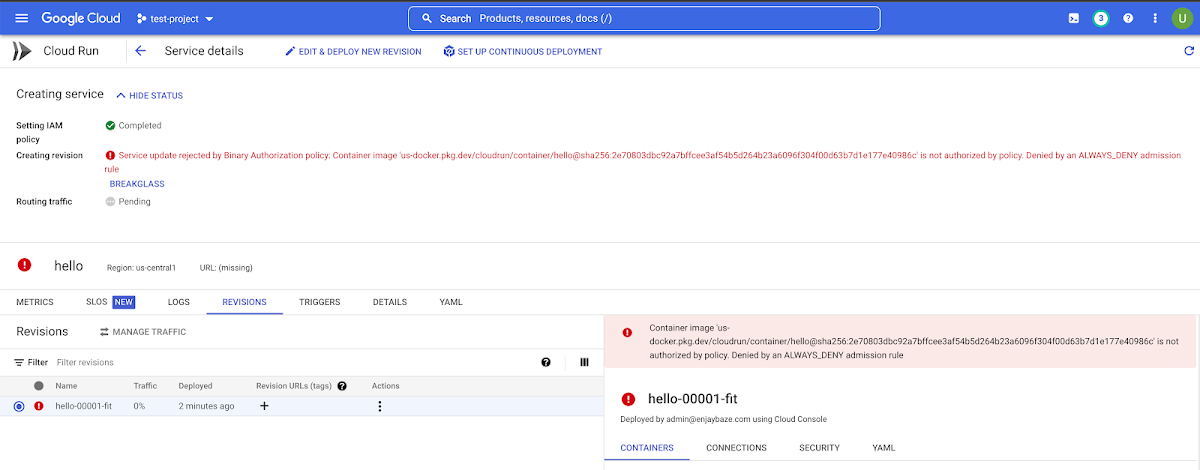
Binary Authorization is a service on Google Cloud that provides software supply-chain security for container-based applications. It enables you to configure a policy that the service enforces when an attempt is made to deploy a container image on one of the supported container-based platforms. It provides an extra layer of security control to ensure only approved container images are deployed on the container platform services like Cloud Run and GKE.
Setting Up Deployment Controls
Now that we are familiar with these services, we can outline how they can be used in conjunction with Cloud Run for enforcing governance control for application deployments.
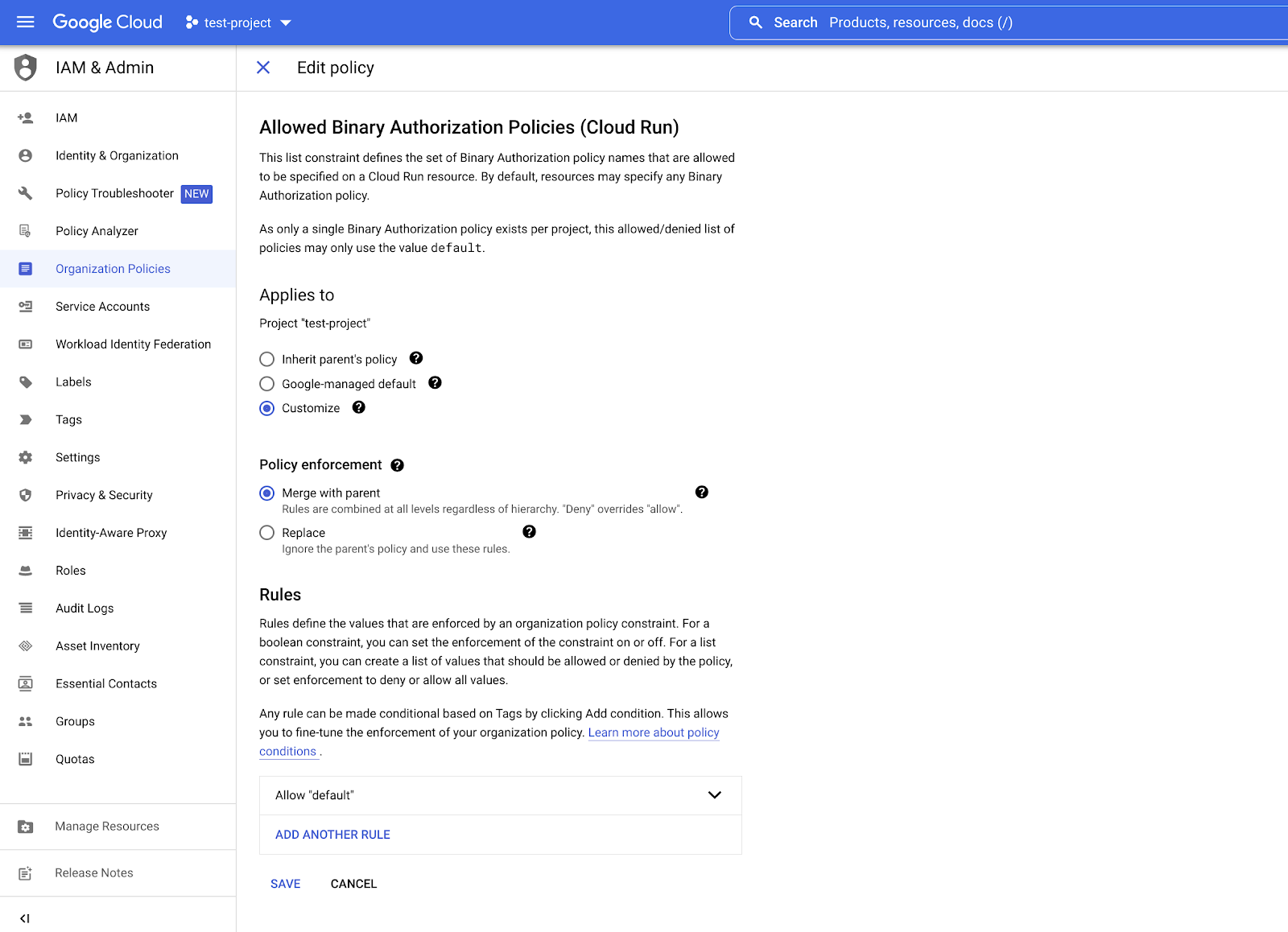
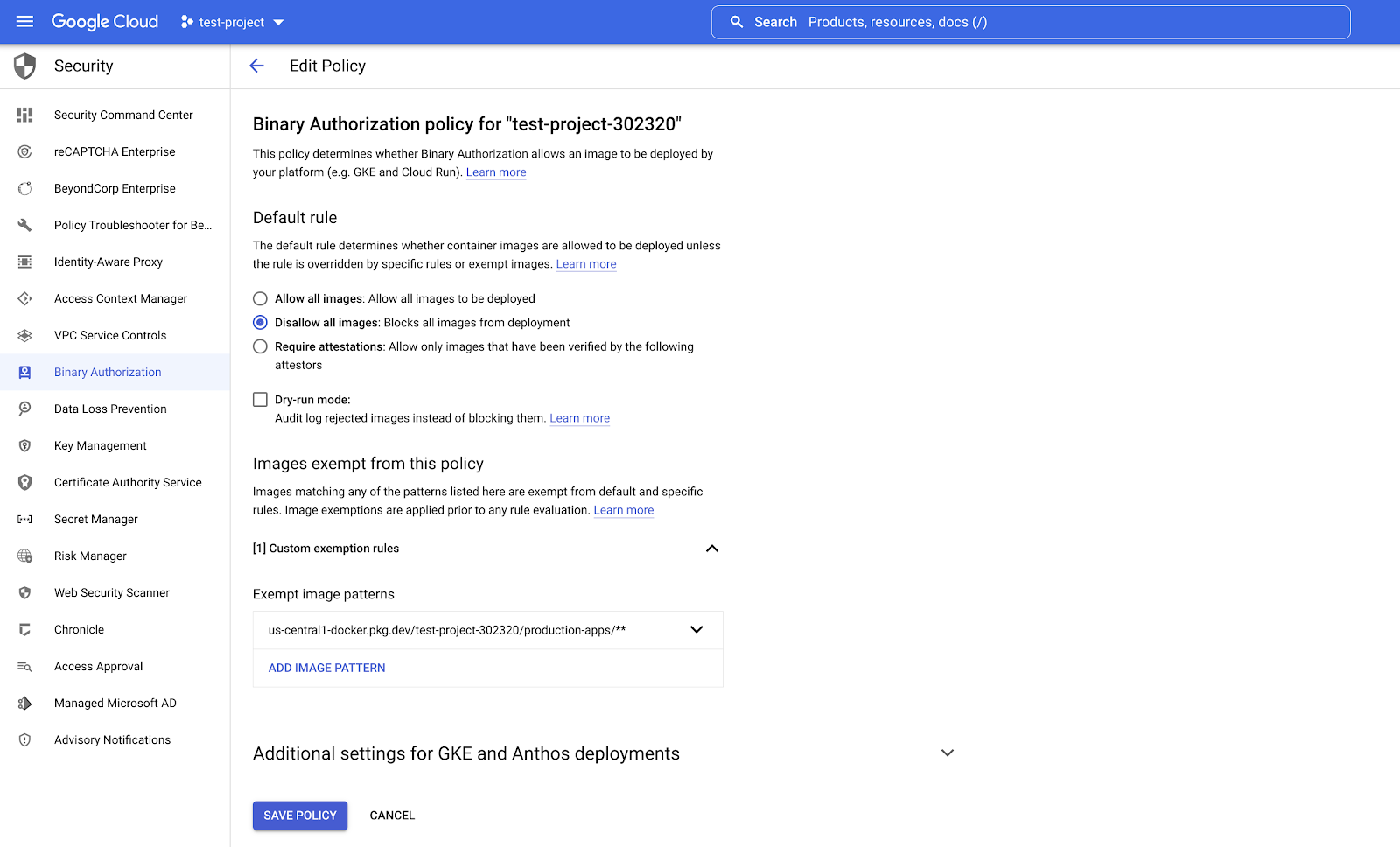
A best practice is to determine the scope of governance control for the organizational policy and the binary authorization policy. The organizational policy lets you define if Binary authorization is required on a specific project e.g. the production project, or on all projects in a specific folder or organization. The Binary Authorization policy grants users the flexibility to enforce deployment from a specific authorized repository in Artifact Registry or from all repositories in an authorized project e.g. the production project . A common use case will be to enforce the organizational policy on a specific project and the binary authorization policy to a single repository.
Step 1: Create a centralized repository in Artifact registry
Based on the needs of your organization, you can create one or more authorized repositories that will host all images that have been approved for deployment. We recommend enabling vulnerability scanning on these repositories to ensure images are monitored automatically for any known vulnerabilities. Push your container images to the authorized repositories and take note of the repository url pattern.
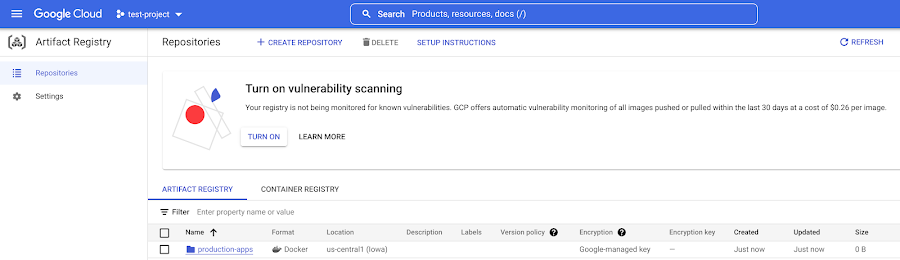
us-central1-docker.pkg.dev/test-project/production-apps/**
in the format
<region>-docker.pkg.dev/<project-id>/<repository-name>
and ** refers to any image with any tag
Conclusion
With Artifact Registry and Binary Authorization, Google Cloud users now have a flexible additional layer of security for better governance of container images. They also have better administration of control on what can be deployed across their container runtime environments. As shown above, organizations can deploy a range of basic to advanced policies depending on the maturity of their security posture or the requirements for different environments. The implementation outlined above can be applied for Google Kubernetes Engine and Anthos deployments with some additional Binary Authorization settings available like continuous validation, specific rules and Google system image exemption. You can find more information on Binary Authorization in our docs.
By: NJ Njoku (Customer Engineer) and Preston Holmes (Product Manager)
Source: Google Cloud Blog
For enquiries, product placements, sponsorships, and collaborations, connect with us at [email protected]. We'd love to hear from you!
Our humans need coffee too! Your support is highly appreciated, thank you!








