If you’ve worked in any facet of IT you know all too well how rapidly technology changes. You’ve probably seen some trendy industry buzz words lately like “cloud native”, “containers”, or “infrastructure as code” just to name a few.
The Cloud
And then there’s “Cloud”—the buzzword to rule them all! If you are coming from a different cloud platform or even an on-prem environment it can be a little intimidating and confusing to get started. Read on to learn how to set up and secure your Google Cloud account and your resources.
A tale of two consoles
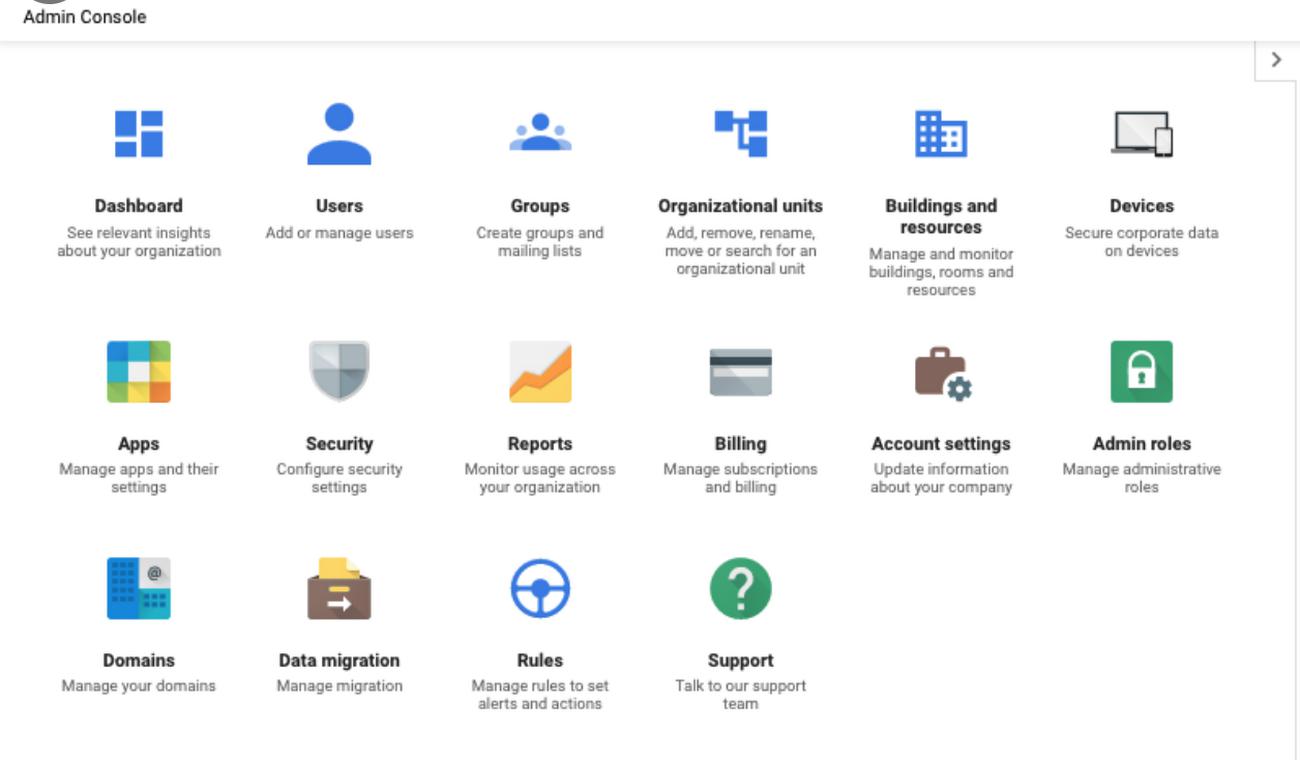
Google Cloud gives you access to two consoles to help secure your account and resources:
- The Admin console: Allows you to manage people, groups, access controls, and Google Workspace domains
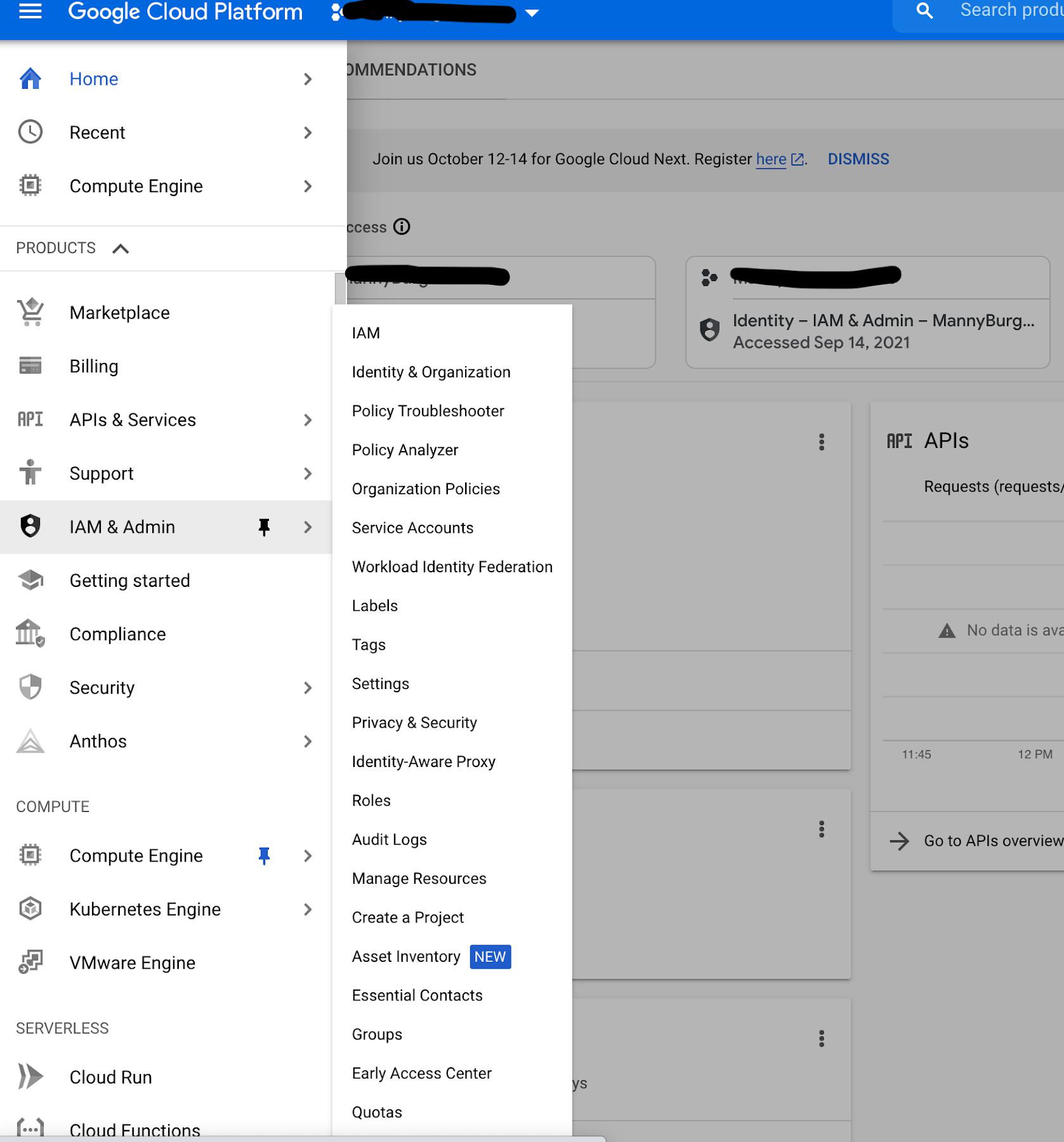
and - The cloud console: Allows you to implement granular access controls via Identity and Access Management (IAM), enable APIs and services, create and manage infrastructure and resources like virtual machines, networking, and much more.
It’s easy to get these two portals mixed up, as they are both so important to managing who can access resources. Let’s take a look at the differences between them and their respective functions.
Our architect
To help us understand the difference we are going to use the help of Ramalton. Ramalton just got a job at a SaaS company called Big Horn Inc. building apps and software specifically for the city of Ramsville. The company is expanding their IT department and hired a cloud architect to help them use Google Cloud and make their applications and infrastructure safer and more reliable.
Ramalton’s first job is to set up the company’s Google Cloud account, so he holds a meeting with the Executive Board of Rams (EBORs) and decides to start with the basics. He proceeds to give a crash course about setting up a Super Admin account and about Identity and Access Management (IAM).
Ramalton goes into detail about how super admins have irrevocable administrative permissions. This option made some executives a little nervous at first, “That’s too much power for one Ram to have,” they said. Ramalton assured them that the super admin account would not be used for the day-to-day administration of the organization; he would set up an org admin account for that. Next he explained to the EBORs how IAM allows Rams to give specific people, groups, or identities access to specific cloud resources or capabilities. IAM gives Rams the ability to keep their cloud infrastructure safe by restricting who can read, edit, or modify it.
So back to our hero…Ramalton’s meeting was a success. The EBORs were very impressed. They wanted to get their Google Cloud account set up right away.
Ramalton’s next tasks: Create the super admin to set up Big Horn’s account, then create users and groups. Ramalton knew that the initial account set up could be done from the Admin console.
What is the Admin console?
The Admin console allows an administrator (like Ramalton) to add users, create groups, manage devices, configure billing, and manage security settings. All these Google Cloud administration tasks can be done from a single location.
Ramalton knew his company was already using Google Workspace so he knew it would be a good idea to set up an organization to manage their Google Cloud account.
What is an organization?
I am glad you asked. An organization is the root node in the Google Cloud resource hierarchy, which means it sits at the top above all your folders, projects, and resources. Existing policies or restrictions made at the organization level are inherited by the folders, projects, and resources below it. Organizations are available for Google Workspace or through Cloud Identity for Google Cloud customers, and you can create an organization today if you don’t have one.
Back to our friend. Now it was time to set up the company’s billing account along with users and groups.
What is a billing account?
In the Google Cloud console, you can set up billing accounts, which allows you to create new services and pay for them, and decide which users in your organization have view-only or admin-access to billing. View-only access allows a user to only see billing details, while admin access allows the user to make changes and/or adjustments to the account billing. It’s a good idea to understand each person’s responsibility in order to give appropriate access as needed. Note that you may have a billing account if you are already a Google Maps Platform customer.
Now that billing has been set up, Ramalton needs to create users and groups in the admin console.
Users
A user is a person that you want to give access to so that they can do a specific task or access specific resources in your account. Under your organization you can invite people to become users.
Groups
Groups are a way to manage users and their permissions. Usually you will put users into groups based on the tasks they normally complete, need to do, or by resources they regularly access. You can attach a role (also known as permissions) to groups. For example if you have several users who only need read-only access to compute resources, you can place them in a group and attach the compute.viewer role to it. Now each user in that group will be able to inherit compute.viewer permissions.
Then it was time for a late day snack. Ramalton headed to the vending machine and decided to buy a bag of salt licks and some grass chips. They were his favorite. While daydreaming Ramalton thought about how he could provide additional security to the company’s Google Cloud account. He decided it would be a good idea to set up some guardrails.
He wanted certain users to only have access to specific services in the company’s account. He found an article on organizational policies, which explained how to set high-level rules that help provide governance within Rams’ account. Organizational policies allow customers to do things like restrict resource creation to certain regions, restrict the APIs that can be enabled, and limit resource creation to only specific configurations.
Ramalton was all done setting up the organization, billing, users, and group and organizational policies. Now he was ready to get into the account and set up the infrastructure so he logged into the Cloud Console.
What is the Cloud Console?
As your main gateway to creating, monitoring, and changing Google Cloud VMs, storage buckets and everything else, the Cloud Console allows you to access and provision a wide variety of services. Within the Cloud Console you will find a navigation menu that logically groups services based on category. The Cloud Console provides the tools and settings you need to configure and secure your applications and the infrastructure they run on.
VPC
Ramalton took a look at his whiteboard, where he took notes from his meeting with the networking and security teams. He remembered they spoke about the need to set up a virtual private cloud (VPC). From an infrastructure networking and security standpoint you will need one or more VPCs to build resources. VPCs allow you to create your own private network within the cloud, set up routing, and define firewall rules.
A VPC is like your own section of a Google datacenter with its own networking that you build your resources in. By default Google Cloud gives you an initial “default” VPC to group your resources. Google Cloud’s best practice is to set up and configure your own VPC, so you can fine-tune your network to your specific needs and maintain complete control over the network.
Authenticating Workloads
Ramalton hears the thud of a hoove bamming on his office door. A burly voice then says, “Hey wassup Ramalton!” It’s his supervisor Ramsey. Ramsey starts to go on and on about how one of his horns is starting to curl and how it’s hard to find hats now. After complaining to Ramalton, he switches the conversation to one of their apps. In Big Horn’s on-prem data center there is an application called Sheepdreams. Sheepdreams keeps track of all the baby sheep that have jumped over the moon. This app is mission critical for Big Horn as it’s their biggest source of revenue.
It helps millions sleep better at night and without it the world as we know it would be doomed. Ramalton needs to give their on-prem database access to a workload in their Google Cloud account. Due to state regulations the customer data needs to stay on-prem. Ramalton doesn’t want to use long lived service keys because they can become a secret management headache. After reading Google Cloud docs, Ramalton thinks that Workload Identity Federation would be a great option to use.
He can use his current on-prem identity provider to call Google Cloud’s short token service (STS) to exchange identities for an access token that will then impersonate a service account configured within his Google Cloud account. This option will allow him to avoid the headache of managing and securing service keys.
Workload identity federation allows external workloads of your applications to securely obtain access to your workload in Google Cloud by providing short lived access as opposed to long lived service account keys.
It’s been a couple of months now and Ramalton has made some really great progress with adapting and using Google Cloud. One day while talking to new manager Hamilton, they began to discuss the newest craze sweeping social media called the tough horn challenge. Hamilton came up with an idea to build an application that would allow rams all over the world to post pictures so they could show how much damage their horns could do. This idea could potentially add a new stream of revenue to Big Horn Inc.
The application would need to have a database, web server, and persistent storage along with load balancing. They wanted to make use of containers because they require less overhead and provide increased portability. Ramalton remembers watching a YouTube video from Google Cloud Next 2018 that highlighted Google Kubernetes Engine (GKE) as a quick and easy way to create and manage containerized workloads. He knew it would be perfect to use for this project because as a container orchestration tool it can deploy, manage, and scale containers. Tools like Google Kubernetes Engine allow Ramalton to create and deploy cloud native applications securely.
Securing all the things
Due to the ongoing pandemic, Ramalton has spent months working from home. He feels confident going back to the office after getting his last dose of the COVID vaccine. Before he could get his hooves in his cubicle, he gets called to the new CISO’s office. He has been impressed with Ramalton’s progress and Google Cloud knowledge and wants help with a new project to modernize Big Horn’s security practices. Recently one of Big Horn’s compute resources was compromised, and an attacker obtained access to company credentials, letting them start some crypto-mining.
Ramir suggested that Ramalton look into using Identity-Aware Proxy (IAP) for access to apps running on Compute Engine instances and secure the apps using identity controls. In addition, Google BeyondCorp Enterprise allows them to give access to critical applications and services whether they run on-prem or in the public cloud. BeyondCorp Enterprise allows access decisions to be made on a per request basis using the context of the request, rather than the network it came from. BeyondCorp Enterprise is flexible, scalable, and most of all, helps secure more than a traditional perimeter model; it also easily integrates with existing device management systems to help make good context-based access decisions.
Get started
Now that you can tell these two consoles apart, frolic freely and secure your Google Cloud account and resources. You can sign up for a Google Cloud account here. Happy clouding!
By: Max Saltonstall (Senior Developer Relations Engineer, Google Cloud) and Emanuel Burgess (Developer Relations Engineer)
Source: Google Cloud Blog
For enquiries, product placements, sponsorships, and collaborations, connect with us at [email protected]. We'd love to hear from you!
Our humans need coffee too! Your support is highly appreciated, thank you!